Malware analysis Malicious activity
4.5
$ 21.99
In stock
(699)
Product Description
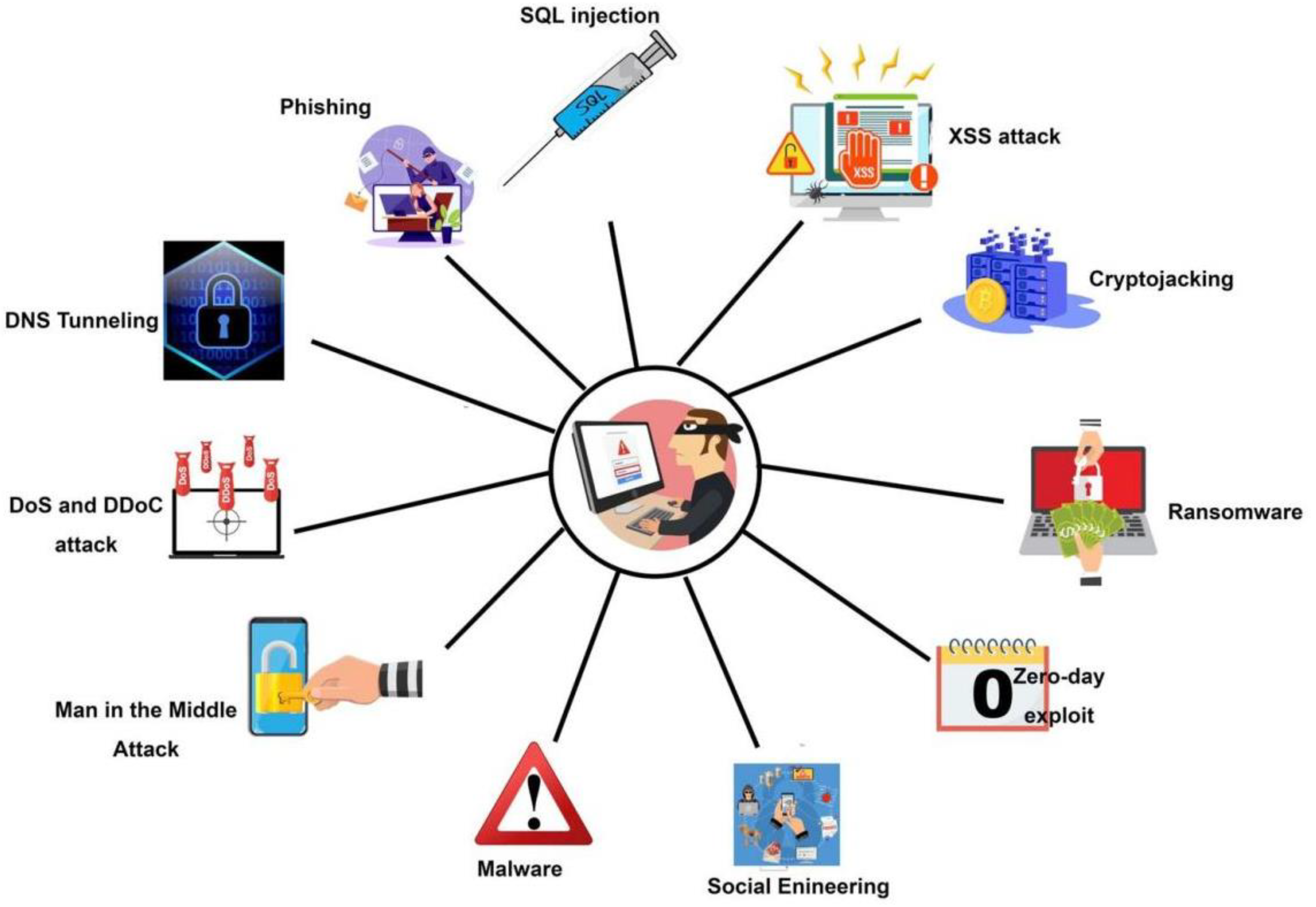
Symmetry, Free Full-Text

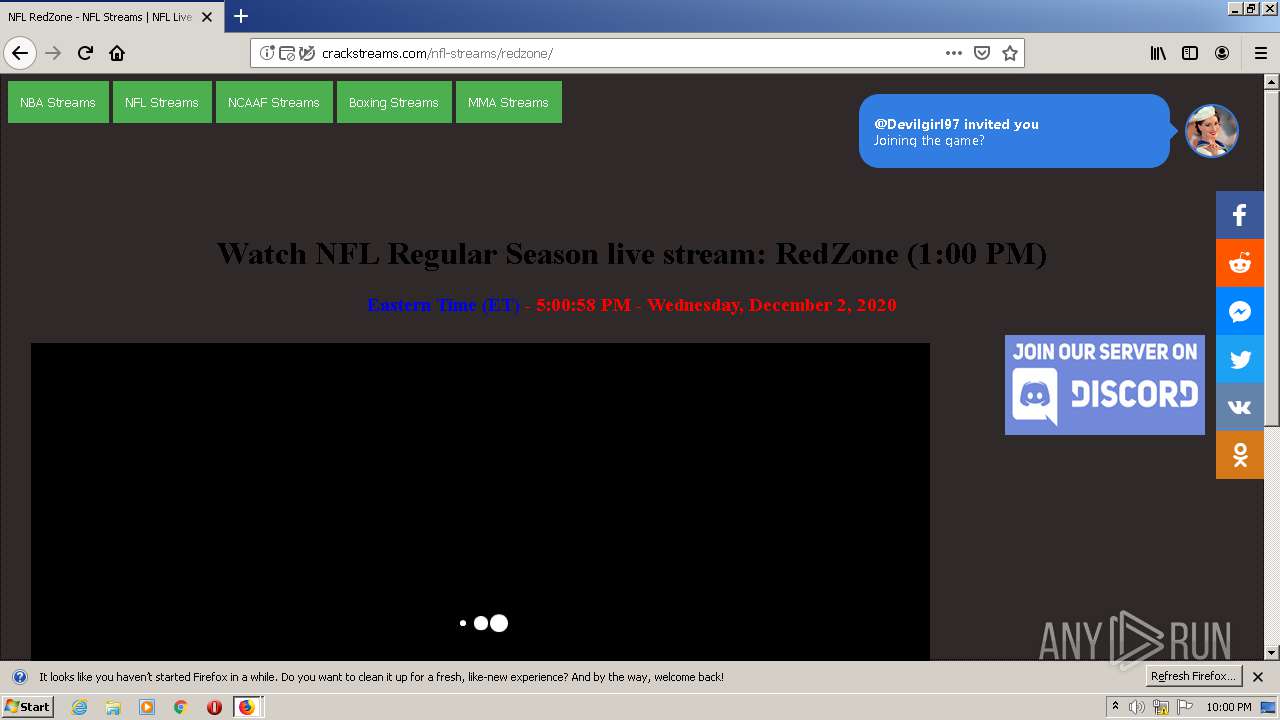
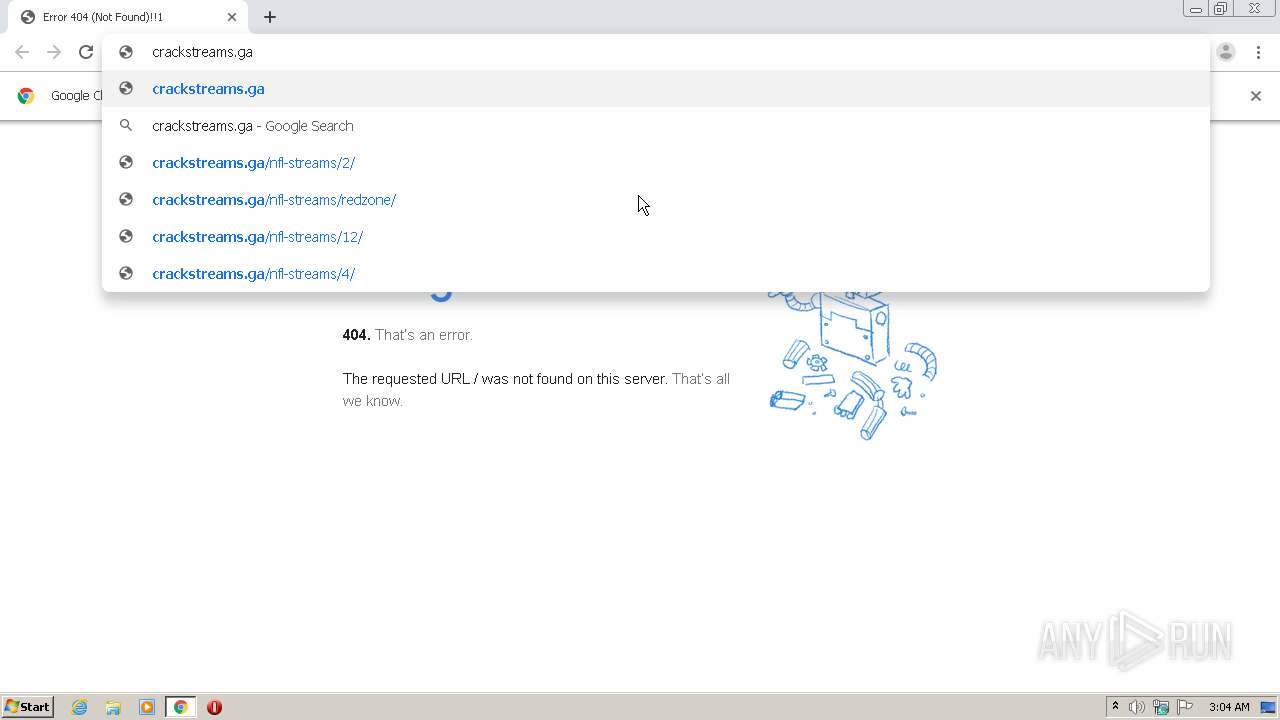
Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Malware Analysis: Steps & Examples - CrowdStrike

Dynamic malware analysis flowchart
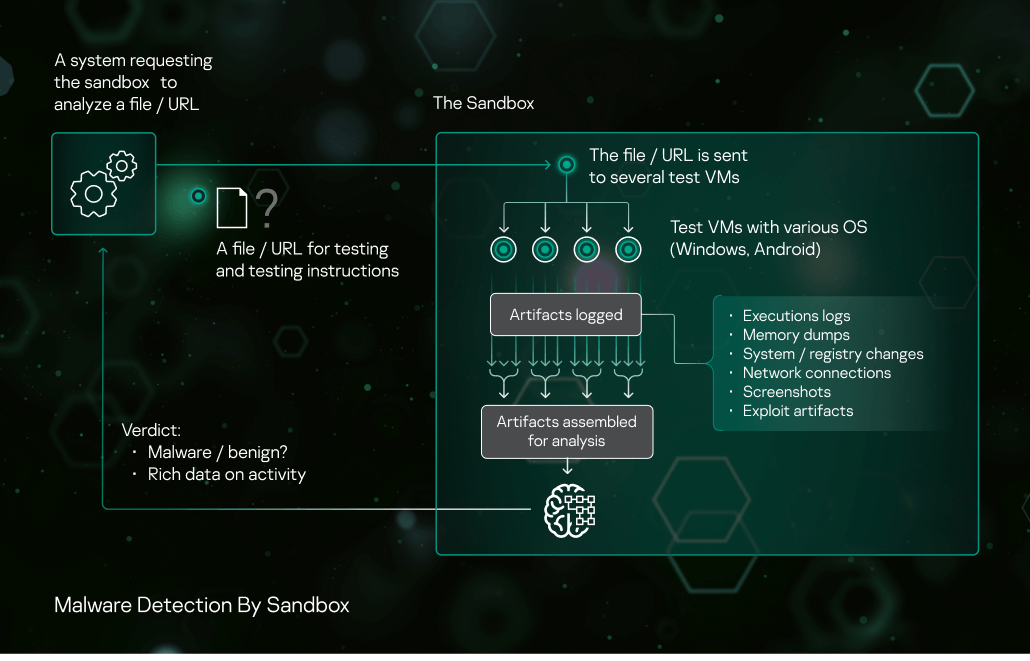
Sandbox Kaspersky

Malware Analysis: Steps & Examples - CrowdStrike
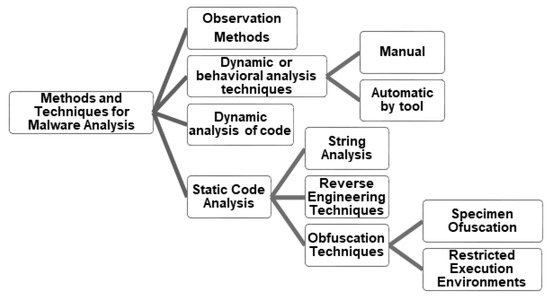
Applied Sciences, Free Full-Text

Is Malware Analysis Right for Your Business?

Malware Analysis: Tips, Tools, and Techniques
Virtualization/Sandbox Evasion - How Attackers Avoid Malware Analysis
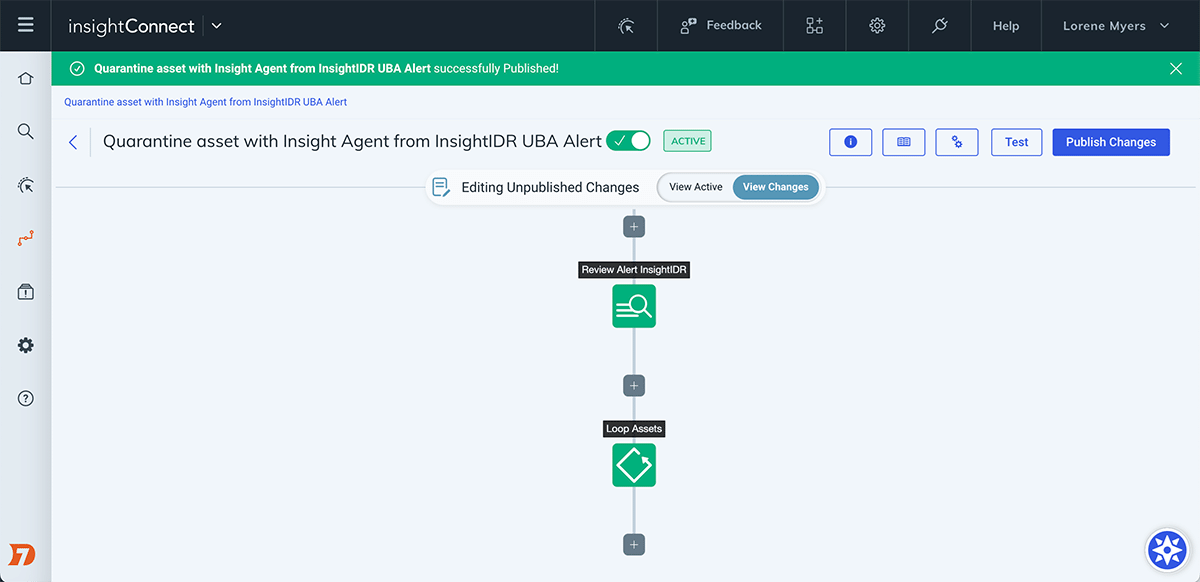
Automate the Investigation and Containment of Malware: InsightConnect
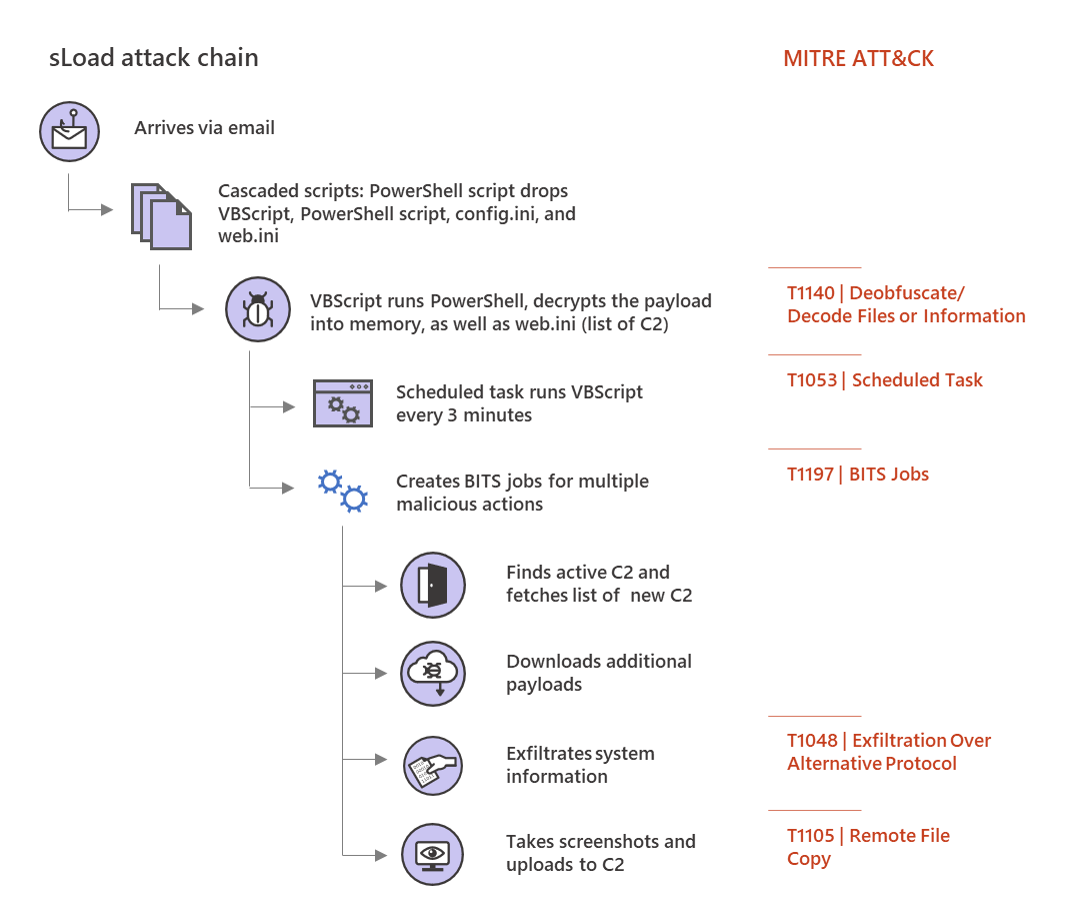
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively for malicious activities
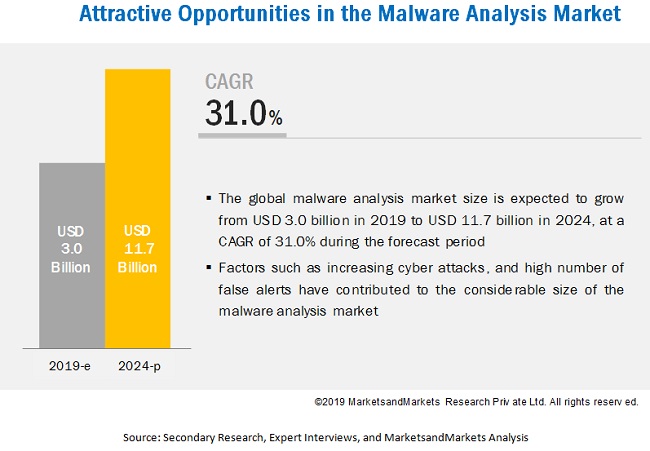
Malware Analysis Market Growth Drivers & Opportunities