Malware analysis
4.6
$ 27.50
In stock
(750)
Product Description
Highlight, take notes, and search in the book

Malware Analysis Techniques: Tricks for the triage of adversarial software
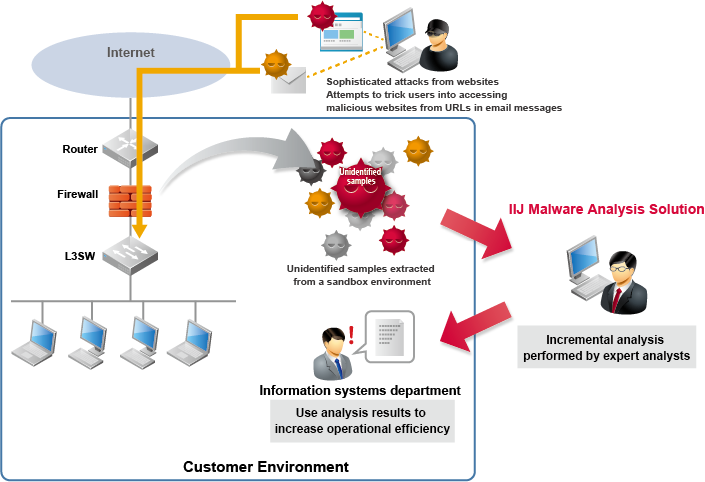
IIJ Malware Analysis Solution, Business

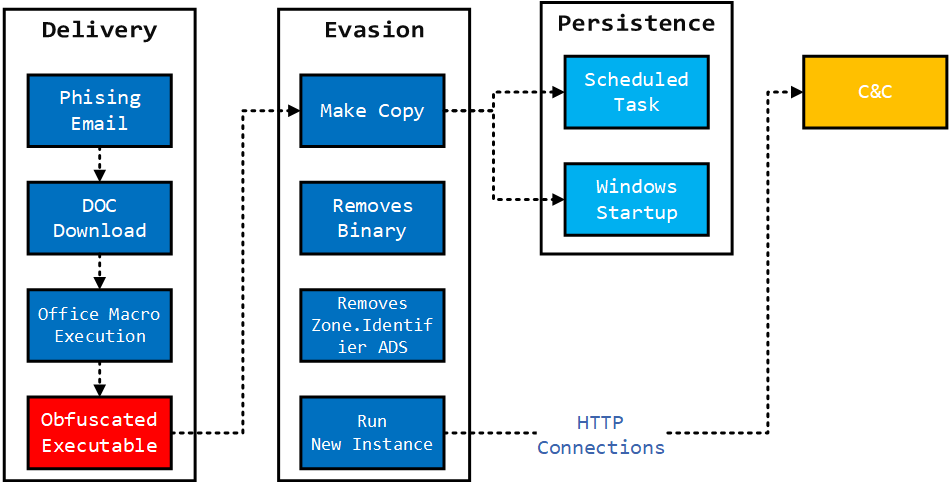
Malware Analysis: SharkBot

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis Benefits Incident Response
Advanced Windows Malware Analysis - Acquiring Memory Artifacts

Malware Analysis Fundamentals

Malware Analysis: Steps & Examples - CrowdStrike

Malware analysis reports

How to Successfully Pursue a Career in Malware Analysis
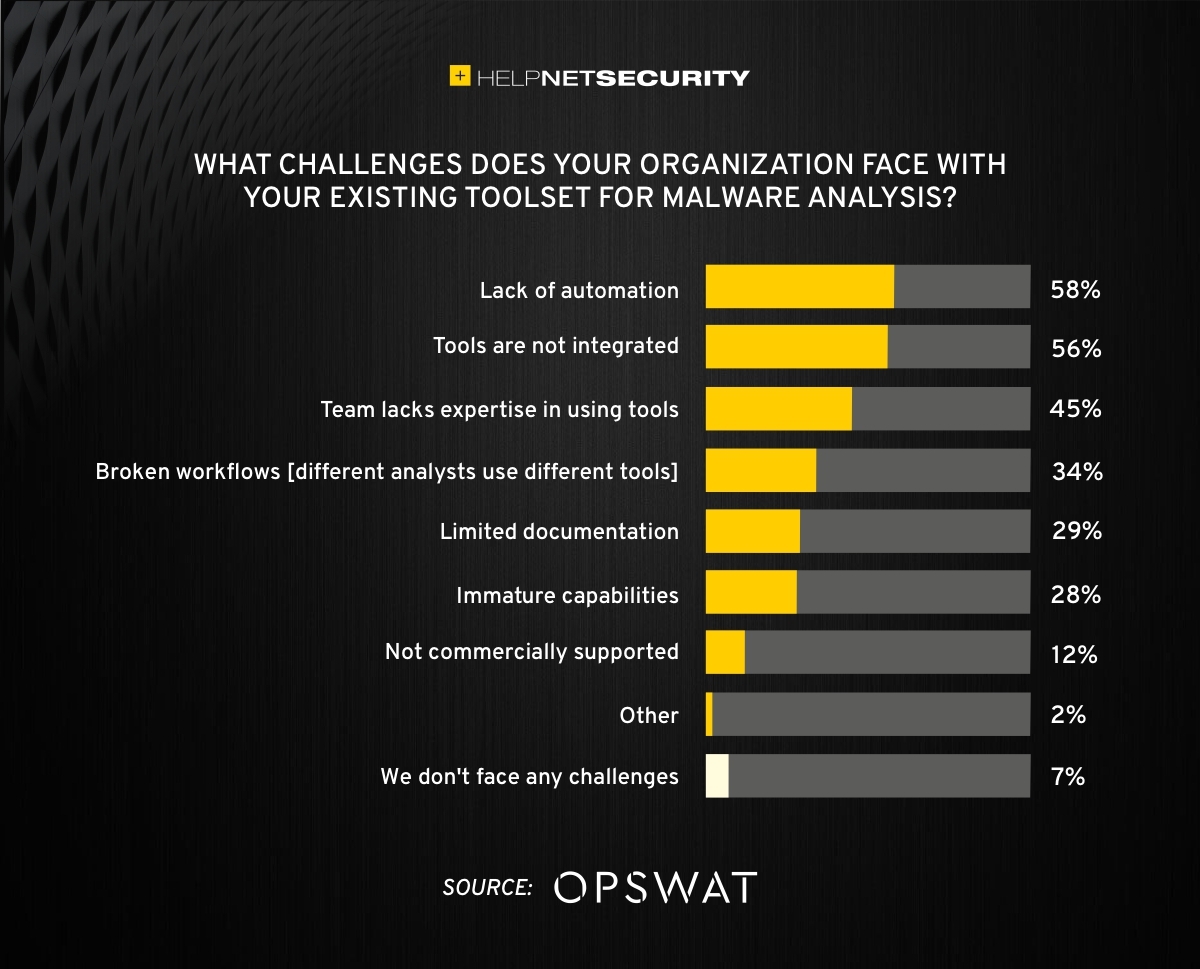
What is challenging malware analysis? - Help Net Security

Detail procedure of malware analysis

How Malware Analysis Works - NetWitness Community - 669511

Malware Analysis: Steps & Examples - CrowdStrike